AWS
VPC - Internet gateways, NAT gateways, Route tables, Subnets
VPC Security - Network ACLs
EC2
1. VPC 생성
name : test-vpc
CIDR : 10.90.0.0/16
2. Internet gateway 생성
Internet gateway
name : test-igw
Internet gateway vpc connect
vpc 연결 : test-vpc
3. Private Subnet, Public Subnet 생성
Private Subnet-01
vpc : test-vpc
name : test-pri-sub01
CIDR : 10.90.10.0/24
Availability Zone : ap-northeast-2b
Public Subnet-01
vpc : test-vpc
name : test-pub-sub01
CIDR : 10.90.1.0/24
Availability Zone : ap-northeast-2a
Public Subnet-02
vpc : test-vpc
name : test-pub-sub02
CIDR : 10.90.3.0/24
Availability Zone : ap-northeast-2b
4. NAT gateway 생성
NAT gateway
name : test-natGateway
subnet
test-pub-sub01
Allocate Elastic IP address
할당 받은 IP를 생성한 NAT gateway에 배정
5. Route table 설정
Private Route table
vpc : test-vpc
name : test-routeTable-pri
explicit subnet association : test-pri-sub01
routes
0.0.0.0/0 - NAT gateway
10.90.0.0/16 local
Public Route table
vpc : test-vpc
name : test-routeTable-pub
explicit subnet association : test-pub-sub01
routes
0.0.0.0/0 - Internet gateway
10.90.0.0/16 local
6. Network ACLs 설정
Private Network ACL
Inbound Rules:
| 100 | HTTP | TCP | 80 | 0.0.0.0/0 | DENY |
| 110 | HTTPS | TCP | 443 | 0.0.0.0/0 | DENY |
| 120 | SSH | TCP | 22 | 0.0.0.0/0 | DENY |
| 130 | Ephemeral | TCP | 1024-65535 | 0.0.0.0/0 | ALLOW |
| 140 | Custom Rule | TCP | 80 | Subnet Range | ALLOW |
| 150 | Custom Rule | TCP | 443 | Subnet Range | ALLOW |
| 160 | Custom Rule | TCP | 22 | Subnet Range | ALLOW |
| * | ALL Traffic | ALL | ALL | 0.0.0.0/0 | DENY |
Outbound Rules:
| 100 | HTTP | TCP | 80 | 0.0.0.0/0 | ALLOW |
| 110 | HTTPS | TCP | 443 | 0.0.0.0/0 | ALLOW |
| 120 | Ephemeral | TCP | 1024-65535 | 0.0.0.0/0 | ALLOW |
| * | ALL Traffic | ALL | ALL | 0.0.0.0/0 | DENY |
여기서 "Subnet Range"는 사용 중인 서브넷의 IP 주소 범위를 의미합니다. 여기선 10.90.10.0/24
Public Network ACL
Inbound Rules:
| 100 | HTTP | TCP | 80 | 0.0.0.0/0 | ALLOW |
| 110 | HTTPS | TCP | 443 | 0.0.0.0/0 | ALLOW |
| 120 | SSH | TCP | 22 | 0.0.0.0/0 | ALLOW |
| 130 | Ephemeral | TCP | 1024-65535 | 0.0.0.0/0 | ALLOW |
| * | ALL Traffic | ALL | ALL | 0.0.0.0/0 | DENY |
Outbound Rules:
| 100 | HTTP | TCP | 80 | 0.0.0.0/0 | ALLOW |
| 110 | HTTPS | TCP | 443 | 0.0.0.0/0 | ALLOW |
| 120 | Ephemeral | TCP | 1024-65535 | 0.0.0.0/0 | ALLOW |
| * | ALL Traffic | ALL | ALL | 0.0.0.0/0 | DENY |
7. Test EC2 생성
ssm-pub 인스턴스를 public 서브넷에 생성
ssm-pri 인스턴스를 private 서브넷에 생성, Key 생성(ssm-test) 후 배정
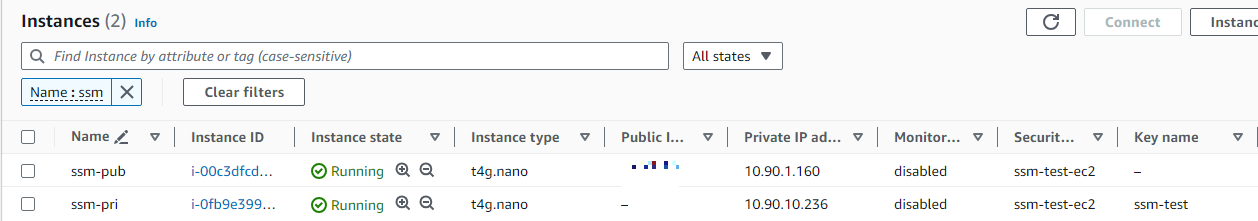
ssm-pub 인스턴스에서 ssm-pri ssh 접속
ssh -i /home/ohsung/ssm-test.pem ec2-user@10.90.10.236
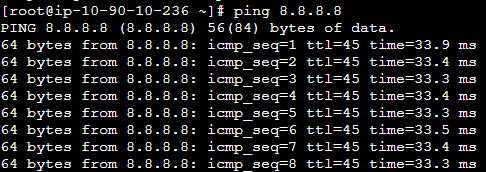
private subnet에 있는 ssm-pri 인스턴스에서 NAT gateway를 통해 인터넷 통신 확인
'Infra > AWS' 카테고리의 다른 글
| Amazon Elastic Container Service - ECS 생성 (0) | 2024.07.30 |
|---|---|
| AWS VPC The maximum number of VPCs has been reached. (0) | 2024.07.10 |
| lambda - available EBS volume 목록 message to slack (0) | 2024.07.04 |
| AWS EC2 자동 실행 정지 Lambda 함수 (1) | 2023.10.24 |
| AWS S3 버킷 생성 JS, React 배포, 데이터 백업 (0) | 2023.10.23 |